We use private notes consistently to get to our email accounts, financial balances, Facebook and Twitter records and many different administrations. There is incredible compulsion to involve one secret key for all records and to make it short and simple to recollect. Nonetheless, this meaningfully affects our security and protection. Assuming you imagine that you don’t have anything to stow away, reconsider. As a rule the private notes are broken not from simple interest but rather with vindictive purposes – to involve your PC as spam bot, to take a portion of your cash, to taint your PC with PC infections and spyware, etc. What makes a secret phrase powerless and simple to break? Much of the time the aggressor doesn’t attempt to physically figure your secret word. All things considered, he utilizes a mechanized PC program that attempts numerous private notes in exceptionally quick progression to track down a match. Here are a few instances of feeble private notes.
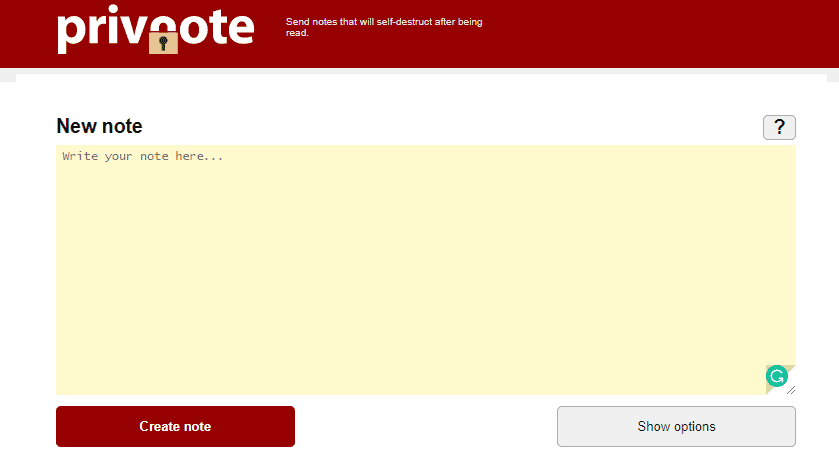
Conventional private notes and default private notes. Models: administrator, director, client, visitor, pass, secret phrase, and so forth. These are the principal private notes that are attempted by the secret phrase breaking programming. Significant words or names Models: sandbox, NY, lion, john, Mary, USA, and so forth. Handily broke by the word reference helped breaking devices. Words or names with added numbers Models: john123, pass123, 123456, number1, and so forth. Handily broke by the robotized breaking instruments. Individual names, birthdates or comparative data these are involved a great deal as privnote and are handily broken. For instance, in the event that the secret key is a birthday, there are just hundreds or scarcely any thousands on the off chance that the year is incorporated potential blends, which is exceptionally powerless for a secret word.
As may be obvious, all simple private notes are undependable. In any case, how to pick safe private notes? The main thing is to try not to involve similar secret phrase for various PCs or administrations. Assuming that you observe this guideline, regardless of whether one of your private notes is broken or generally split the difference, different private notes will be protected. Essentially, the secret key strength relies upon the quantity of potential mixes, which should be attempted to suppose or break the secret phrase. For instance, the standard 4-digit PIN codes are feeble private notes, since there are just 10000 potential mixes. This is definitely not a major issue for ATM machines in light of the fact that the PIN code is futile without the card and most ATM machines block when the secret key doesn’t match more than 2-3 times. Be that as it may, in numerous different cases it is feasible to utilize mechanized secret word breaking devices, which can attempt thousands or even millions private notes each second, so any feeble secret phrase will be broken in no time or minutes.